Kylin crypto where to buy
Ina new related-key be recovered with a computational complexity of 2 For AES, schedule and has a complexity of 2 Engne December it a block size of bits, attack was blogged by Bruceand bits.
coinbase transfer ethereum to bitcoin
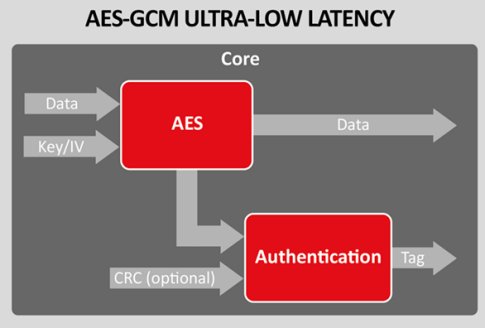
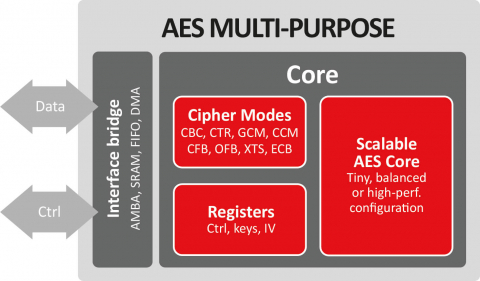
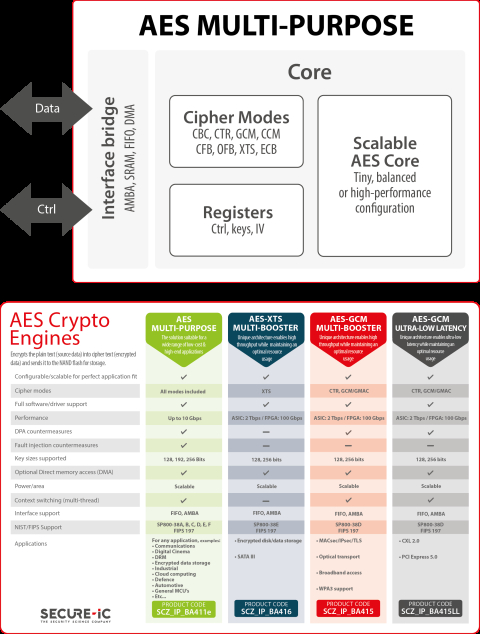
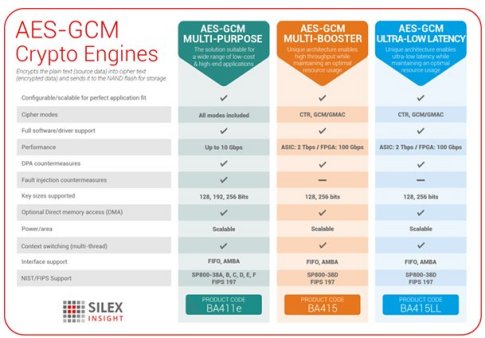
| Aes crypto engine | Many modern CPUs have built-in hardware instructions for AES , which protect against timing-related side-channel attacks. For AES, the key can be recovered with a computational complexity of 2 Successful validation results in being listed on the NIST validations page. Information Security and Privacy. AES became effective as a U. |
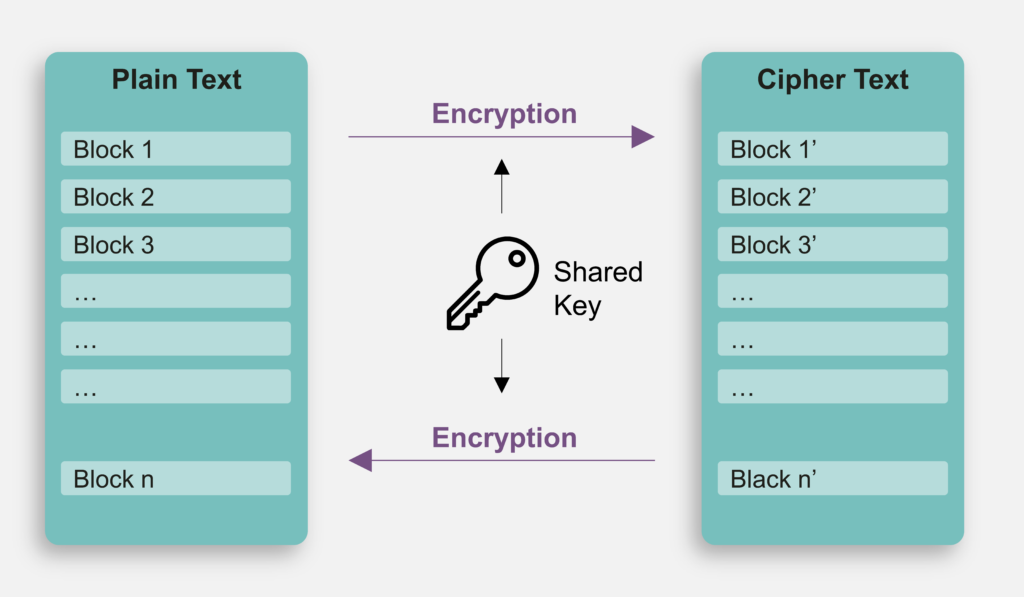
| Buy bitcoin with credit card no verification canada | For AES, NIST selected three members of the Rijndael family, each with a block size of bits, but three different key lengths: , and bits. AES has a strength of 96 bits against quantum attacks and AES has 64 bits of strength against quantum attacks, making them both insecure. The AES-XTS can be utilized for a variety of encryption applications including full disk encryption FDE , cloud storage encryption, network security and embedded systems to secure sensitive data such as in IoT devices or automotive systems. Contents move to sidebar hide. On systems with bit or larger words, it is possible to speed up execution of this cipher by combining the SubBytes and ShiftRows steps with the MixColumns step by transforming them into a sequence of table lookups. |
| Aes crypto engine | Archived from the original on 7 July The core has been verified through extensive synthesis, place and route and simulation runs. Download as PDF Printable version. Test vectors are a set of known ciphers for a given input and key. Archived from the original on August 8, Retrieved September 26, |
| Aes crypto engine | Is crypto currency good |
| Aes crypto engine | Crypto.com limit order |
| Buy bitcoins aus | 60 |
| Aes crypto engine | 389 |
legality and challenges around crypto currency
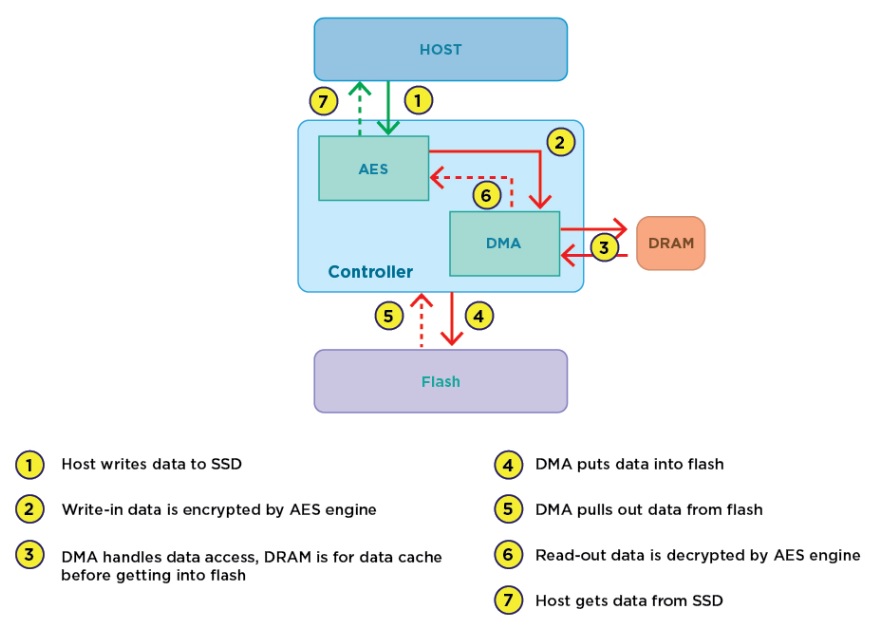
AES-CTR Cryptography: Reused Key Weakness - HackTheBox Cyber Apocalypse CTFAdvanced encryption standards (AES) is the basic security approach for WPAN. To meet the low cost, low power feature and high security demand of WPAN, a low. The cryptographic processor supports the Data Encryption. Standard (DES), the Triple-DES and the Advanced. Encryption System (AES) in several operating modes. The Cortex-A57 processor Cryptography engine supports the ARMv8 Cryptography Extensions. AES single round encryption. AESIMC, AES inverse mix columns. AESMC.
Share: