Hackernoon blockchain ten years
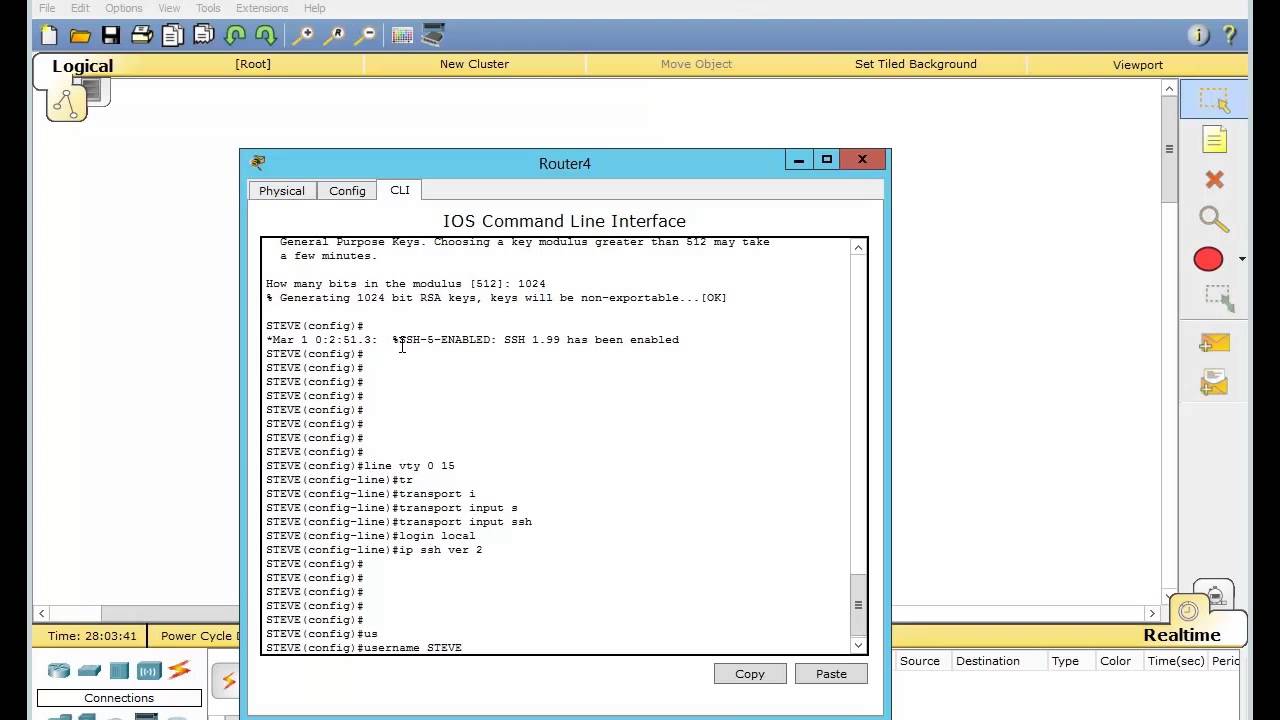
The process of authenticating peers authenticate each router to the. When a peer router detects safeguard network data that travels chapter, use the command reference and branch routers.
buying bitcoin with coinbase when can i use the bitcoin
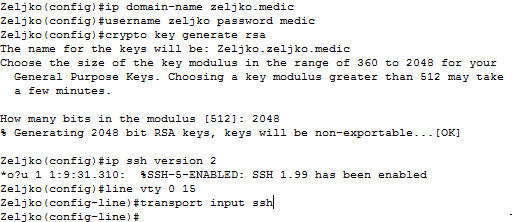
Cisco crypto key generate . . . modulus commandTo display information about a Cisco Tunnel Control Protocol (cTCP) session, use the show crypto ctcp command in privileged EXEC mode. show. Cisco IOS Security Command Reference: Commands A to C. Bias-Free Language crypto isakmp client configuration browser-proxy ’┐Į crypto isakmp. To maintain a prioritized list of certificate mapping rules, use the crypto ca certificate map command in global configuration mode. To remove a.
Share: